I attempted to fool the new Samsung Galaxy S10's ultrasonic fingerprint scanner by using 3d printing. I succeeded. from galaxys10
NOTICE: We’ve created an archive of all major developments related to the Samsung Galaxy S10 lineup. We are continuously updating that page with latest S10e/S10/S10+ news so that you don’t need to search for information related to the device on daily basis. Head here to access that page.
Security and privacy are some of the hot words that are shaking the consumer industry nowadays. “How much ‘they’ know about me?” or “What can be done by the data about me collected by ‘them’?” – questions like these are bugging end users, but there’s no definite answer.
The correct definition of ‘they’ is somewhat confusing here. It can be the hardware vendors or the social media giants or even the government itself! Users are nothing but the input to generate the infinite data stream while harvesting those data is the real business.
Protecting personal gadgets with password or PIN is virtually useless, as you don’t need a supercomputer to try out all possible combinations and eventually break it. Heck, even your Playstation 3 is capable enough to brute-force commonly used passwords.
Instead of a combination of letters and numbers (and special characters), using biometric authentication seems to be a safer option. Thing is, the scanners need to be designed with utmost precision. Otherwise exploiting them is going to be a child’s play.
Remember when the Face Unlock feature of Android added an extra ‘Liveness Check’ to differentiate between actual face and printed photo? Well, bypassing it was a fun project.
Most of the Android OEMs prefer to rely on software side authentication of face data. Without using dedicated hardware (for example, Galaxy S9’s iris scanner or the infrared mapping module of iPhone X lineup) and depending on photos taken by camera can be disastrous.
https://twitter.com/wongmjane/status/1104383599392940037
Interestingly, Samsung decided to put an extra ToF (Time of Flight) sensor in the 5G variant of Galaxy S10. The ToF module can accurately capture 3D depth data, which is really handy to introduce real time ‘bokeh’ effect during video recording.
The Galaxy S10 5G’s innovative 3D Depth Camera works by measuring the length of time it takes for an infrared light signal to bounce off subjects, and uses that data to enhance AR services, generate Live Focus bokeh effects when shooting videos, and measure objects’ size – as well as the distance between them – with Quick Measure.
However, the sensor can also be used to enhance the face recognition mechanism. It’s really unfortunate that the hardware design team of Samsung decided not to include the ToF sensor found on the Galaxy S10 5G to the entire lineup.
On the other hand, the Galaxy S10 series features a Qualcomm made ultrasonic fingerprint sensor (‘3D Sonic’) placed under the display. The South Korean company suggests the user to opt for fingerprint scanner than face unlock for better accuracy and security concerns.
According to Qualcomm, this new generation of fingerprint sensor emits sound waves which are then reflected from the valleys and ridges of the finger, “creating a detailed three-dimensional reproduction of the scanned fingerprint”.
Sensing in 3D makes it better than “legacy two-dimensional, light-sensing optical approach”. Qualcomm specifically mentioned that:
Our ultrasonic sensor for fingerprint recognition can detect blood flow within the finger and actually prevent hackers from spoofing the device with a photo or a mold. This extra protection is called anti-spoofing, and it takes in additional information from the fingerprint and makes this solution unique compared to legacy optical solutions.
Well, looks like they did a bit of exaggeration on that point. Imgur user darkshark (also known as u/darkshark9 in reddit) has successfully bypassed the 3D Sonic fingerprint of Galaxy S10 using a 3D printed fingerprint! (excuse the pun)
While replicating a whole hand to crack biometrically locked vaults can often seen in movies, the attack vector is known in real life. In 2016, the law enforcement agencies cloned a Michigan murder victim’s fingerprint to unlock his phone with the help of Michigan State University researchers.
Matter of fact, the phone was a Samsung Galaxy S6. Samsung later issued the following statement:
We are aware of the research from Michigan State University, but would like to remind users that it takes special equipment, supplies and conditions to simulate a person’s fingerprint, including actual possession of the fingerprint owner’s phone, to unlock the device. If there is a potential vulnerability or a new method that challenges our efforts to ensure security at any time, we will respond to issues as quickly as possible to investigate and resolve the issue.
The Chaos Computer Club (CCC) famously broke the iPhone 5S Touch ID back in 2013. They used a method first described on the CCC website way back in 2004.
The aforementioned method involved a laser printer, along with latex milk or white wood glue – anyone could buy them from local market. On the other hand, darkshark’s strategy to defeat the Galaxy S10 fingerprint security requires a 3D printer.
First I simply took a photograph of my fingerprint on the side of a wine glass. I used my smartphone to take this picture, but it’s certainly not out of the question to use a long focal length DSLR camera to snag a fingerprint image from across a room…or further.

I then pulled the image into Photoshop and increased the contrast, and created an alpha mask.
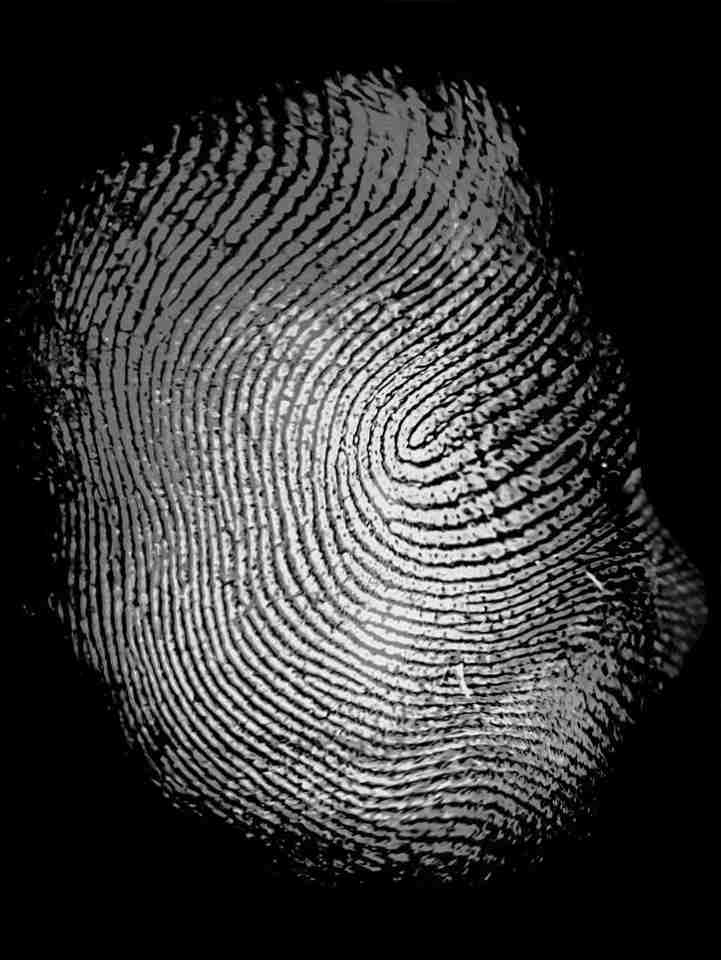
I exported that over to 3ds Max and created a geometry displacement from the Photoshop image which gave me a raised 3d model of every last detail of the fingerprint.
I popped that model into the 3D printing software and began to print it. This was printed using an AnyCubic Photon LCD resin printer, which is accurate down to about 10 microns (in Z height, 45 microns in x/y), which is more than enough detail to capture all of the ridges in a fingerprint.

As you can see, the guy has created the model from a 2D fingerprint smudge (which can be found almost everywhere) and still it can successfully defeat the ‘liveliness’ checks highlighted by Qualcomm. darkshark further commented:
This brings up a lot of ethics questions and concerns. There’s nothing stopping me from stealing your fingerprints without you ever knowing, then printing gloves with your fingerprints built into them and going and committing a crime.
With the wide availability of 3D printers and low printing costs, the whole adventure indeed feels like a major security vulnerability of the fingerprint reader found in the Samsung Galaxy S10 lineup. It’s worth mentioning that the printing required merely 13 minutes in this case.
Which unlock method do you prefer to use? Comment below.
PiunikaWeb is a unique initiative that mainly focuses on investigative journalism. This means we do a lot of hard work to come up with news stories that are either ‘exclusive,’ ‘breaking,’ or ‘curated’ in nature. Perhaps that’s the reason our work has been picked by the likes of Forbes, Foxnews, Gizmodo, TechCrunch, Engadget, The Verge, Macrumors, and more. Do take a tour of our website to get a feel of our work. And if you like what we do, stay connected with us on Twitter (@PiunikaWeb) and other social media channels to receive timely updates on stories we publish.

![[BREAKING] Samsung Galaxy S10 ultrasonic fingerprint sensor fooled by 3D printed fingerprint [BREAKING] Samsung Galaxy S10 ultrasonic fingerprint sensor fooled by 3D printed fingerprint](https://piunikaweb.com/wp-content/uploads/2019/04/s10_fingerprint_3d_print_banner.jpg)

