New updates are being added at the bottom of this story…….
Original story (published on January 07, 2020) follows:
Samsung, like many other Android vendors, has this habit of cramming plenty of features into its phones, some of which are gimmicky while others have proven to be quite useful over time.
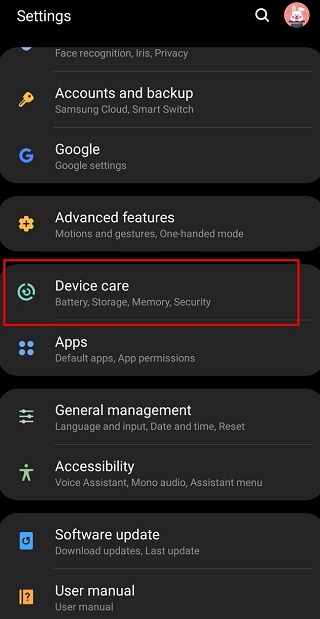
In the latter camp is the little-known Samsung Device Care that is hidden in the Settings menu of all the latest Samsung Galaxy phones. With this tool, you can improve the performance of your device as well as clear up some storage space when needed.
Although quite a handy tool, it is the Storage Cleaner feature of Device Care that is causing uproar in the online Samsung community.
The feature scans your device’s internal storage to dig out all dormant apps and any other unnecessary data stored on the device which then can be deleted to free up space. Apparently, Samsung partnered with a Chinese company known as Qihoo 360 to create the Storage scanner.
Notice a certain “powered by 360” under the Storage section in the Device Care? Look closely in the screengrab below and you should be able to see it in the red rectangle.

For the uninitiated, Qihoo 360 is a Chinese software company whose shady deals are well documented. The company is known to develop software accused to be spyware thanks to the willingness to give the Chinese government access to any of its stored data.
Considering that this same company is behind the tool that has full access to data stored on your device, many owners of Samsung phones are left wondering why they paid a premium for their devices.
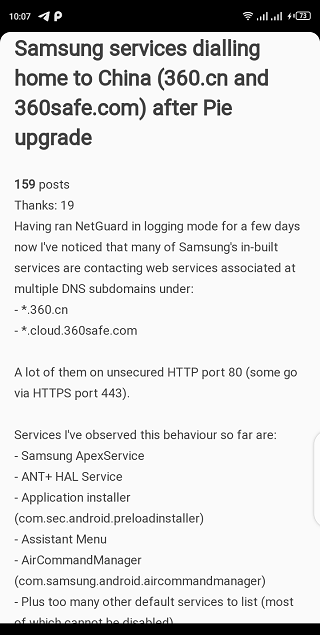
Not long ago, a Redditor published a detailed post on Chinese spyware pre-installed on all Samsung phones and tablets. Below is a summarized version.
The storage scanner in the Device Care section is made by a super shady Chinese data-mining/antivirus company called Qihoo 360. It comes pre-installed on your Samsung phone or tablet, communicates with Chinese servers, and you CANNOT REMOVE it (unless using ADB or other means).
He was able to establish that indeed the Storage scanner was communicating with Qihoo 360 servers when in active use.
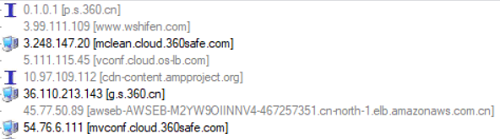
Unfortunately, though, it wasn’t possible to determine the exact information that was being shared between the devices. But what is known is that this isn’t the first time Qihoo 360 has been accused of the same behavior on Samsung phones.
In fact, back then (early 2019), it was claimed that this behavior was also noted in plenty of other pre-installed services namely Samsung ApexService, ANT+ HAL Service, Application installer, Assistant Menu, and AirCommandManager, among others.
Whether the Storage cleaner is the only loophole here remains to be seen. But we cannot rule out the prospects of Qihoo 360 having access to plenty of other data on your Samsung Galaxy device.
The fact that these services are so deeply integrated into the phone means simply uninstalling them is not an option, at least not without going the ADB way or other possible routes. It remains to be seen what Samsung has to say about these allegations, but a statement is expected.
Update (January 08, 2020)
Samsung has responded with a statement in the official Samsung Members app (Korea), distancing itself from claims that Qihoo 360 software installed on Galaxy phones could be sending data to servers in China.
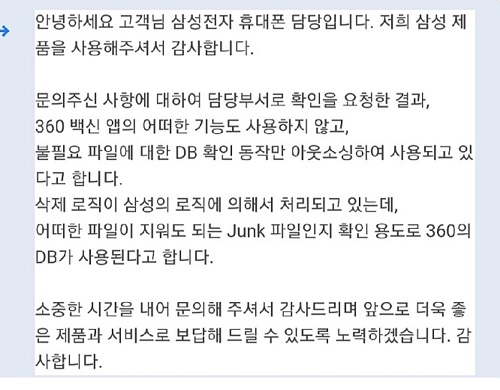
In a loosely translated statement, Samsung says Qihoo 360 software is only used to verify unnecessary/junk files by running the data through its (360) database. In the process, no personal data is shared between the servers, so there is nothing to worry about.
We should probably get an official statement from the company soon and when it arrives, we will update this post with the details.
PiunikaWeb started as purely an investigative tech journalism website with main focus on ‘breaking’ or ‘exclusive’ news. In no time, our stories got picked up by the likes of Forbes, Foxnews, Gizmodo, TechCrunch, Engadget, The Verge, Macrumors, and many others. Want to know more about us? Head here.

![[Response] Samsung Galaxy phones come preinstalled with potential spyware from China's Qihoo 360 [Response] Samsung Galaxy phones come preinstalled with potential spyware from China's Qihoo 360](https://piunikaweb.com/wp-content/uploads/2020/01/Samsung-Galaxy-A51.jpg)

