Android users for decades have had the SMS feature. The feature was very useful initially, but after the advent of social messaging apps, it lost relevance. Still, Google continued to offer the SMS feature with almost no improvement.
Apple, on the other hand, presented its users with iMessage, an updated version of SMS with all modern-day features. Apple’s iMessage works across all Apple devices, is encrypted and above all, carriers have no control over how it works. This has made Android users felt left out.

Google, on its end, has long been making efforts to provide Android users with an iMessage-type service. And, it finally succeeded last month, when it formally announced the roll-out of RCS (Rich Communication Services).
This RCS messaging service is the successor to SMS, and like other third-party messaging services offers all modern features, including better group chats, typing indicators, read receipts, sharing of files and high-quality images.
Further, the RCS messaging is based on the user’s phone number, meaning, if you are texting someone who also has the RCS, the feature will automatically turn on in the chat. Also, unlike the SMS that depends on the carrier’s cellular connection, RCS uses a data network.
Means, you can send it over WiFi, as well. Another benefit that RCS holds over SMS is that it supports more characters per message. Moreover, it supports Group messages with up to 100 participants.
Despite the benefits that RCS messaging offers to the users, it appears to be a threat to the users in terms of security. The first security concern is that the RCS is not end-to-end encrypted like iMessage. This means it is relatively easier for hackers to snoop on your messages.
An even bigger security threat is raised by researchers from SRLabs, who claim that RCS implementations lack uniformity in terms of security measures.
This could compromise user data, including user location, contents of text messages and more, researchers told Motherboard in a phone call.
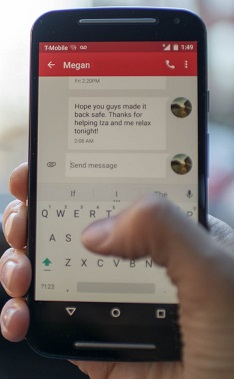
The issue is not with the RCS standard. But, what is really putting users at risk is the implementation of the RCS messaging by the carriers. Since many of the RCS standards are undefined, companies deploy their own way of implementation and this increases the chance of things going wrong.
Many carriers use smartphone owners’ IP address for identification and based on this, provide the corresponding configuration file. However, as per the research firm, any app on a user’s phone can access this file, and it needs no extra permission for that.
This means any app could sneak on your login credentials for all the text messages and voice calls. Moreover, they could easily track a user’s location and know if they are online.
Karsten Nohl from SRLabs said:
I’m surprised that large companies, like Vodafone, introduce a technology that exposes literally hundreds of millions of people, without asking them, without telling them
Another loophole in the implementation of the RCS is when the carrier sends RCS users a six-digit verification code. According to the researchers, any hacker could gain access to the security code using brute force attacks. And, it won’t take more than five minutes for a hacker to get access to a user’s RCS profile.
This means hackers can take over user accounts as RCS does not do sufficient validation of user identify, domains, and certificates. Because of this, a hacker can bypass the domain name, and could even spoof caller ID to pretend to be someone else.
Moreover, the vulnerability could even allow hackers to know a one-time password that is sent via SMS. This would allow hackers to carry unauthorized bank transactions, or even take control of the user’s account. Nohl said:
All of these mistakes from the 90s are being reinvented, reintroduced
They further added:
It is being rolled out for upwards of a billion people already who are all affected by this.
Though it seems to be a major security threat, for now, there is no evidence that hackers have done any such thing. Hopefully, researchers would reveal more information when they talk about the findings at the Black Hat Europe conference in December.
A good thing is that the carriers are aware of this. So, we can expect the issue to be resolved very soon, but that does not mean the users who are already using RCS are safe. Google’s RCS has already been enabled by about 100 carriers in the US and Europe.
SRLabs did not reveal the name of the carriers with faulty RCS implementations. So, it is possible that the hackers may exploit the vulnerability until carriers roll out the fix. Until then, users are certainly not safe.
According to SRLabs, these vulnerabilities can be patched. The researchers have also provided a few suggestions, such as using strong one-time password codes and taking information from the SIM card to verify the user.
Several carriers told Motherboard that they are aware of the findings by SRLabs, and are reviewing it. Vodafone said that they already have many protections in place for RCS, and that it would review the new findings, and would take actions if needed.
We will review these protections in light of the research and, if required, take any further protective measures
If RCS messaging service aims to compete with Apple’s iMessage, then it is very important that all such vulnerabilities are patched quickly. Smartphone owners would only use RCS freely if they have trust in the service that their data and information is safe.
What can you do until the vulnerabilities are patched?
Since SRLabs has not revealed the name of the carriers with unsafe RCS, there is no way of knowing who could be at risk. There might not be any evidence that hackers have actually exploited these vulnerabilities, still to be on the safe side, all you can do is disable RCS until the fix is rolled.
PiunikaWeb started as purely an investigative tech journalism website with main focus on ‘breaking’ or ‘exclusive’ news. In no time, our stories got picked up by the likes of Forbes, Foxnews, Gizmodo, TechCrunch, Engadget, The Verge, Macrumors, and many others. Want to know more about us? Head here.