Modern age instant messengers play a crucial role in the society. Thanks to the enormous growth of social media and rise of privacy concerns, more and more such platforms are moving towards end-to-end encryption, compelling support for anonymity and endorse the freedom of speech.
Russian entrepreneur Durov brothers founded Telegram, which is now a household name among human rights activists across the world. Of course you can set up your own weed channel by utilizing the extensive privacy minded features, but let’s keep that aside for now.
Telegram requires the phone number of the users to create and (optionally) authenticate their accounts. It can be possible to hide the phone number from your account info, but there is a catch!
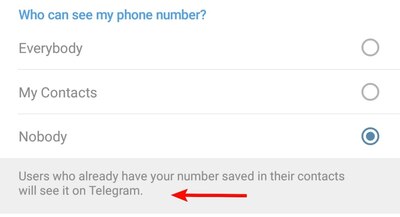
Q: Who can see my phone number?
On Telegram, you can send messages in private chats and groups without making your phone number visible. By default, your number is only visible to people who you’ve added to your address book as contacts. You can further modify this in Settings > Privacy and Security > Phone Number.
Note that people will always see your number if they know it already and saved it in their address book.
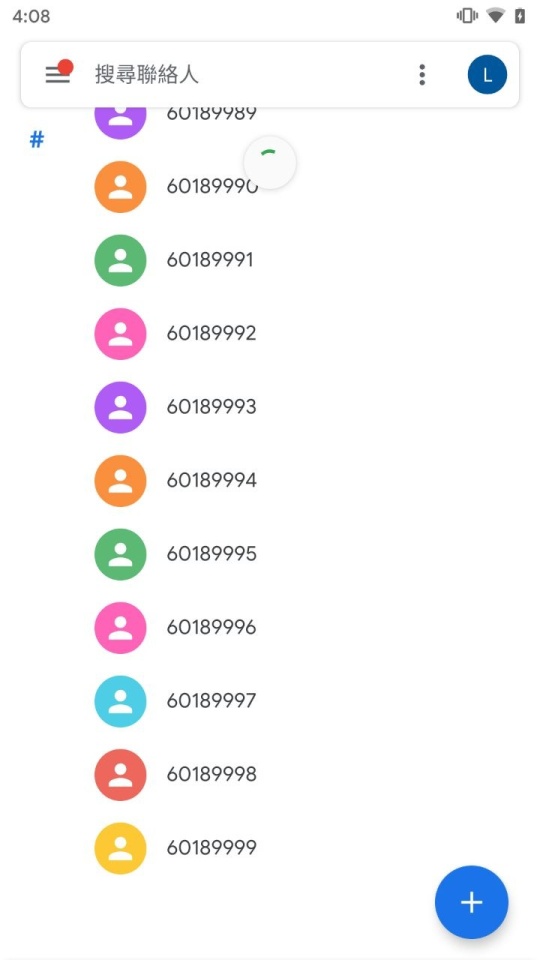
Apparently this design can be used to circumvent the privacy wall of Telegram owners, especially in sensitive scenarios. A rogue user can add a bunch of sequential numbers in phonebook. Afterwards they can connect it with a public channel and sync the contact info.
Guess you can already speculate the outcome. Telegram will give the attacker all the contact details of those entities whose number is in that list after syncing. In case the rogue one is a law enforcement agency, findling the person behind that number is a child’s play.

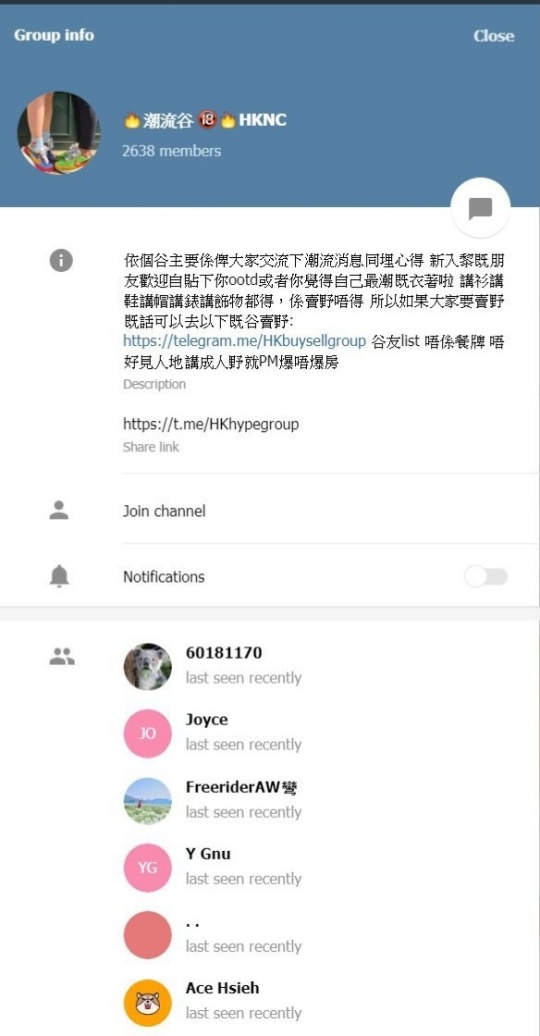
The Hong Kong anti-extradition bill protesters are mostly dependent on Telegram due to the advantages like massive scalable Supergroups and the privacy factors. The bug was first discovered in LIHKG, a popular online forum destination for Hong Kong residents.
Independent security researchers also confirmed the attack vector, and there is no easy way to patch it without requiring the background logic of the IM itself. In case of Hong Kong protestors, they are advised to use burner SIMs as shifting to another platform is not feasible.
1. Alice, a Telegram user, is in a public group named CommonsGroup
2. Alice do not want anyone to see her phone number in Telegram. So, she hide her phone number in Telegram’s privacy settings. (Privacy > Phone Number > Nobody)
3. Mallory, the attacker, want to uncover the real identity of members in CommonsGroup.
4. Mallory adds large number of phone numbers sequentially to the address book on her phone, assuming Alice’s phone number is in the list. (we have tested adding 10,000 phone numbers)
5. Mallory syncs her contacts with Telegram
6. Mallory joins CommonsGroup (which is public)
Expected Result
Alice’s phone number will never be shown in Telegram group info because she has set the phone number privacy to Nobody.
Actual Result
Mallory can see Alice’s phone number in Group info. In theory, if Mallory adds enough phone numbers, she can uncover the phone number of any members in public groups. It is a real threat for us because the space for phone number in Hong Kong is limited
At this moment, Telegram does not want to call the situation as ‘bug’ as their official FAQ does explain the limitation of the phone number hiding functionality.
A few months ago, Telegram suffered from a state-sponsored DDoS attack. Allegedly there was strong correlation between that attack and the Hong Kong protest. The situation is far more chaotic this time, as the lives of the protestors might be jeopardized.
PiunikaWeb is a unique initiative that mainly focuses on investigative journalism. This means we do a lot of hard work to come up with news stories that are either ‘exclusive,’ ‘breaking,’ or ‘curated’ in nature. Perhaps that’s the reason our work has been picked by the likes of Forbes, Foxnews, Gizmodo, TechCrunch, Engadget, The Verge, Macrumors, and more. Do take a tour of our website to get a feel of our work. And if you like what we do, stay connected with us on Twitter (@PiunikaWeb) and other social media channels to receive timely updates on stories we publish.



